This phrase consists of four four five six random words in a phrase. It should be easy to remember but hard to guess, making it a good password.
at ten billion guesses/sec
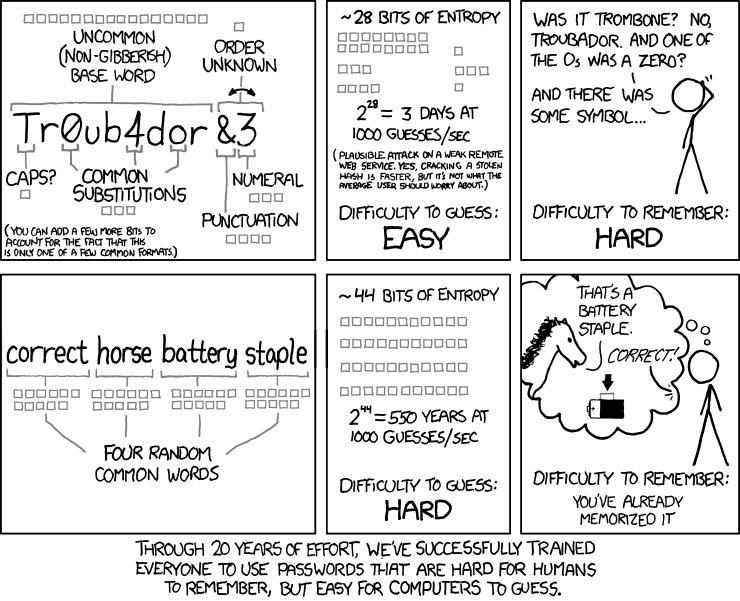
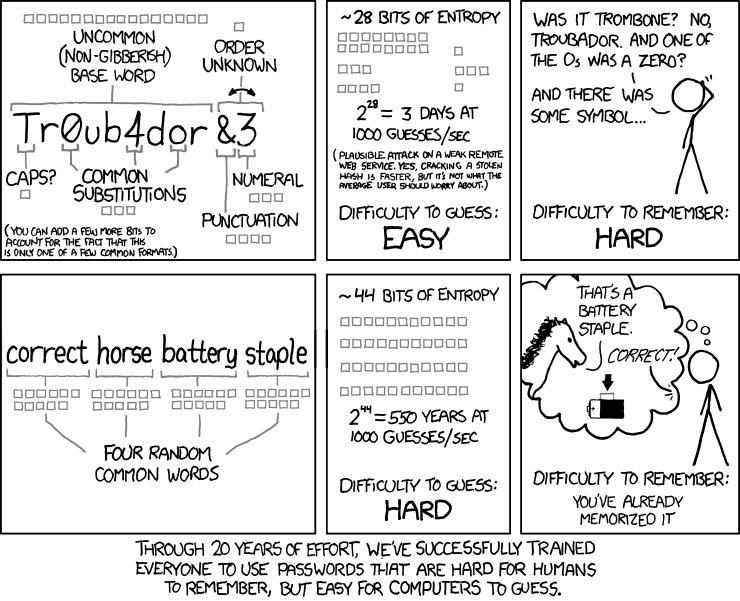
Inspired by the following xkcd comic strip:
More information
- Check if your existing passwords have been compromised at haveibeenpwned.com
- All computation is done locally in your browser using javascript, no passphrase data is sent or received from any server
- The randomness comes from the cryptographically secure getRandomValues function
- Time to guess estimate assumes offline cracking a weak hash of the passphrase at ten billion guesses per second. This is conservative, but is plausible given how often password data breaches happen and the doubling of computer speed each year.
- Common word list contains 2075 words, derived from the 10,000 most common passwords which were words in a dictionary but not swear words or proper nouns.
- View the source code on GitHub. It is purposefully simple to allow easy verification.
- Donations accepted via Bitcoin: 1FZcTQUjxDhnbA658GuoLEzqTan9VtiUP8